The Mac Endpoint Security Problem: Why Cross-Platform EDR Falls Short on macOS
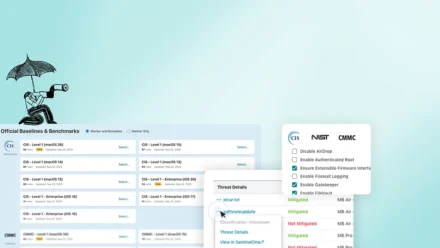
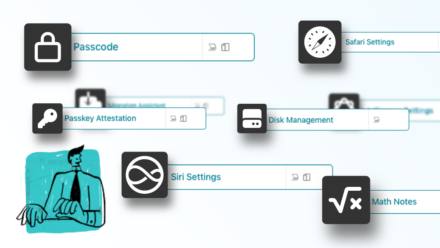
Not all EDR tools are built equal — especially on Mac. If your endpoint security runs the same way on macOS as it does on Windows, you’re likely paying for blind spots. This post breaks down the real difference between EDR and MDR, where cross-platform tools fall short on Apple devices, and why Apple-first security built into your management workflow is the smarter path to closing compliance gaps and cutting SOC overhead.